
NetIQ® Secure Configuration Manager™
Finds and repairs configuration errors that lead to security breaches or downtime. Using NetIQ® Secure Configuration Manager™ helps you to enforce security configuration policy across critical systems in evolving IT environments. Start reducing your risk of security breaches, failed audits, or costly downtime.
(Note: Latest Update – NetIQ has joined Micro Focus. NetIQ is now part of Micro Focus.)
Your organization faces increased security risks and compliance challenges when it loses visibility and control of sensitive data due to evolving and complex threat and regulatory environments. Using NetIQ® Secure Configuration Manager™ helps to protect sensitive data by enabling you to enforce security policy across critical systems. The solution proactively assesses system configurations in light of regulatory requirements and your organization’s security policies, alerting teams to instances in which system configurations drift from policy, helping them to re-mediate mis-configurations before they result in security breaches or failed audits. Manager Finds and repairs configuration errors that lead to security breaches or downtime.
NetIQ® Secure Configuration Manager™ provides the comprehensive configuration assessment and reporting capabilities necessary for compliance with the Sarbanes Oxley Act (SOX), Payment Card Industry Data Security Standard (PCI DSS), the Health Insurance Portability and Accountability Act (HIPAA), the Health Information Technology for Economic and Clinical Health Act (HITECH), the Federal Information Security Management Act (FISMA), North American Electric Reliability Corporation Critical Infrastructure Protection (NERC CIP) and more. Extensive automation for assessment and reporting not only reduces the strain on IT resources but also helps ensure that critical systems routinely meet compliance standards.
Multiple regulatory compliance mandates? No problem.
Ensuring regulatory compliance in a heavily regulated industry can be an overwhelming task.
What if you could achieve your compliance objectives using the resources you have?Now you can with NetIQ® Secure Configuration Manager™
NetIQ® Secure Configuration Manager™ helps organizations meet their security and compliance goals by delivering:
■ Vulnerability assessment—identifies host flaws by assessing them against security intelligence delivered by an automated service and reports on the frequency and location of vulnerabilities.
■ User entitlement reporting—assesses user permissions for access to critical information, providing answers to your questions about who has access to what level of critical information.
■ Baselining and delta reporting—reports changes to system and user configurations, highlights instances in which configurations drift from policy, provides the security information your team needs to quickly remediate poor configurations.
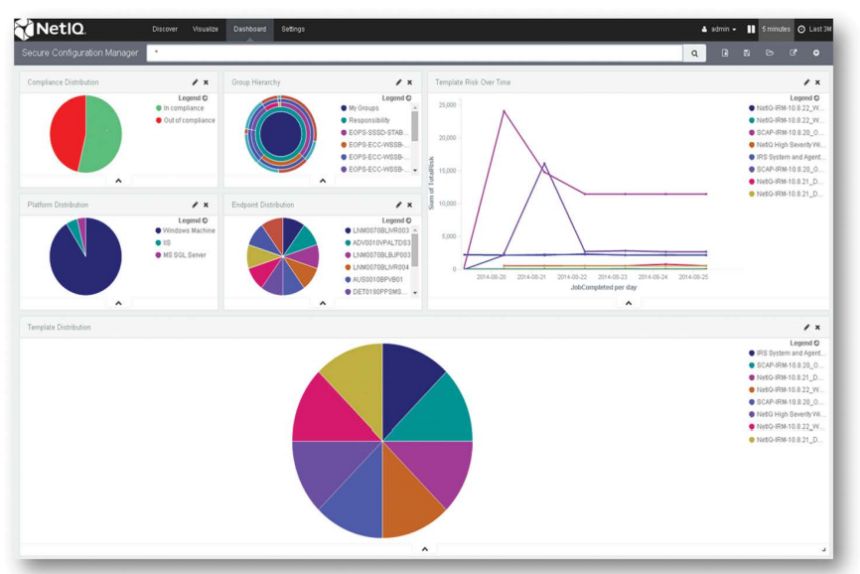
■ Security and Compliance Dashboard— quickly visualize and communicate configuration compliance and risk status with robust drill-down options and dynamic reporting.
■ Business exception management— ensures that the risk from excluded systems or checks is properly understood, managed and documented by security teams.
When stakeholders say “show me,” you can. NetIQ® Secure Configuration Manager™
– streamlines risk and compliance reporting, enabling you to produce assessments that prove you are working with the business to mitigate risks.
By using Secure Configuration Manager you can protect sensitive data and avoid non-compliance with corporate and regulatory policies.
Key features include:
■ Out-of-the-box compliance and best practices knowledge to simplify the process of setting appropriate system configurations.
■ Broad platform and application support, including Microsoft Windows, UNIX, Linux, IBM iSeries and System i, Oracle, and Microsoft SQL Server and Internet Information Services (IIS). Expanded support for network devices from Cisco Systems and Juniper Networks.
■ Automated delivery of the latest vulnerability, threat and patch information.
■ Report scheduling to automate when and how often Secure Configuration Manager performs assessments.
■ Agent or agentless operating system, database and application assessments.
■ “Grade”-based risk scoring provides reliable metric for tracking progress against known best practice configurations.
■ Built-in exception management capabilities to manage information security risks associated with known exceptions.
■ Security Content Automation Protocol (SCAP) validation to ensure your compliance assessment solution is in compliance with federal requirements.
■ Integration with IT GRC solutions using the UCFinterchange to ensure a common language helps teams provide automated, continuous monitoring and reporting to key stakeholders.
For further information on NetIQ® Secure Configuration Manager™ click here

